


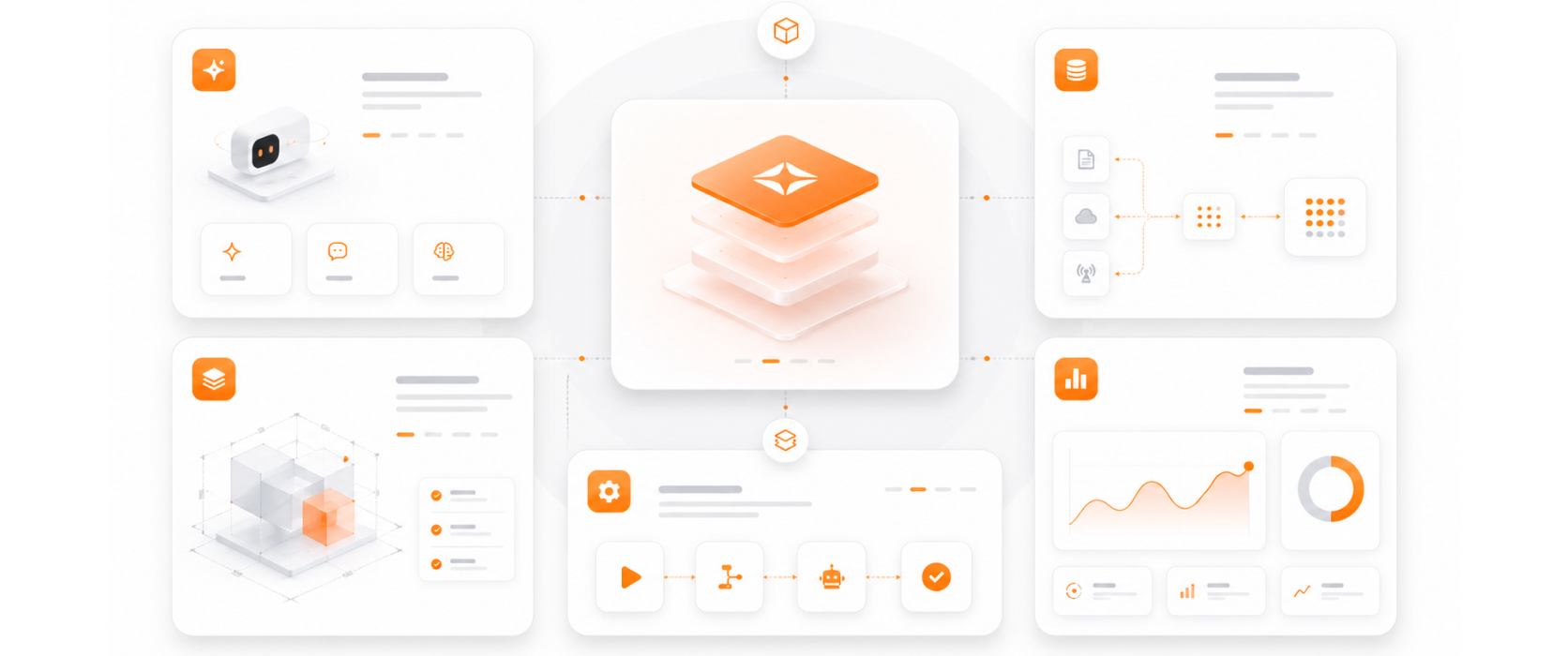
Validated delivery methodology for enterprise cloud security implementation.
We implement Microsoft's native security tooling — Sentinel, Defender for Cloud, and Defender for Cloud Apps — integrated with your existing Microsoft investment.
We establish a Secure Score baseline and track improvement over time — making security investment visible and measurable.
Sentinel deployments with custom detection rules, tuned for your environment — reducing false positive noise and improving real threat signal.
Automated compliance scanning against CIS Benchmarks, ISO 27001, and other frameworks — continuous evidence of security compliance for auditors.